Stop Reacting to Threats & Start Hunting Them
Integrated & Intelligent
Cerebral is an AI-powered security platform that integrates User & Entity Behavior Analytics (UEBA) with User Activity Monitoring (UAM), allowing rapid Data Breach Response (DBR). The ability to hunt threats by proactively recognizing signs of risk, like changes in an employee’s attitude and behavioral patterns, allows you to move your security posture from reactive to proactive.
Unlike network monitoring or document tracking, Cerebral immediately alerts you to who is exhibiting signs of risk, shows you related screen shots so that you can immediately determine the true nature of the incident. This visibility empowers your IT security team to rapidly take action (with 100% confidence) all while gathering the evidence essential to taking legal action.
Best Insider Threat Solution 2020
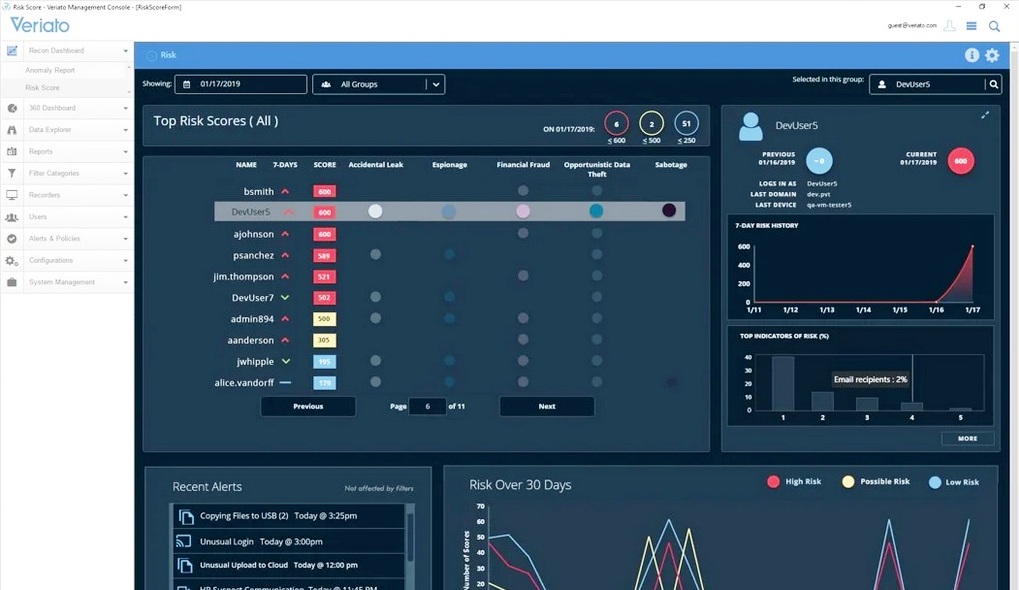
Cerebral’s Risk Scoring
At a glance, you’ll see all individual’s with elevated levels of risk. This daily Risk Scoring maximizes efficiency and productivity by allowing your security team to hunt threats proactively.
Cerebral’s AI-based behavior analysis continually tracks each user's activity and language to create their daily risk score. The Risk Score dashboard shows high scores for each day, trends, recent alerts, and user details. It provides an immediate overview of high risk, user behavior within your organization.